Microsoft’s April 2024 Patch Tuesday Addresses 147 CVEs (CVE-2024-29988)
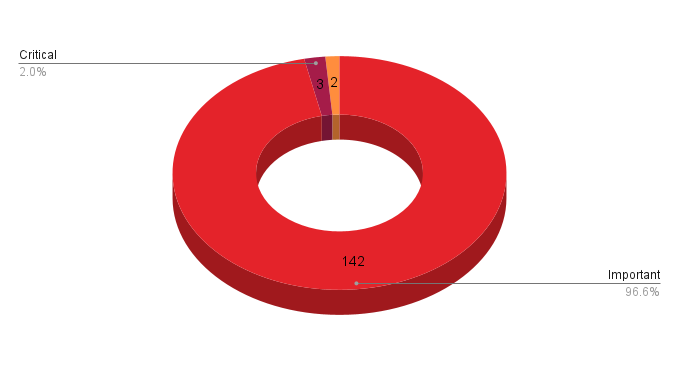
- 3Critical
- 142Important
- 2Moderate
- 0Low
Microsoft addresses 147 CVEs in its April 2024 Patch Tuesday release with three critical vulnerabilities and no zero-day or publicly disclosed vulnerabilities.
Update April 10: The blog has been updated to include reference to exploitation for CVE-2024-29988 and the addition of CVE-2024-26234.
Microsoft patched 147 CVEs in its April 2024 Patch Tuesday release, with three rated critical, 142 rated as important, and two rated as moderate.
This month’s update includes patches for:
- .NET and Visual Studio
- Azure
- Azure AI Search
- Azure Arc
- Azure Compute Gallery
- Azure Migrate
- Azure Monitor
- Azure Private 5G Core
- Azure SDK
- Intel
- Internet Shortcut Files
- Microsoft Azure Kubernetes Service
- Microsoft Brokering File System
- Microsoft Defender for IoT
- Microsoft Edge (Chromium-based)
- Microsoft Install Service
- Microsoft Office Excel
- Microsoft Office Outlook
- Microsoft Office SharePoint
- Microsoft WDAC ODBC Driver
- Microsoft WDAC OLE DB provider for SQL
- Role: DNS Server
- Role: Windows Hyper-V
- SQL Server
- Windows Authentication Methods
- Windows BitLocker
- Windows Compressed Folder
- Windows Cryptographic Services
- Windows DHCP Server
- Windows DWM Core Library
- Windows Defender Credential Guard
- Windows Distributed File System (DFS)
- Windows File Server Resource Management Service
- Windows HTTP.sys
- Windows Internet Connection Sharing (ICS)
- Windows Kerberos
- Windows Kernel
- Windows Local Security Authority Subsystem Service (LSASS)
- Windows Message Queuing
- Windows Mobile Hotspot
- Windows Proxy Driver
- Windows Remote Access Connection Manager
- Windows Remote Procedure Call
- Windows Routing and Remote Access Service (RRAS)
- Windows Secure Boot
- Windows Storage
- Windows Telephony Server
- Windows USB Print Driver
- Windows Update Stack
- Windows Virtual Machine Bus
- Windows Win32K - ICOMP
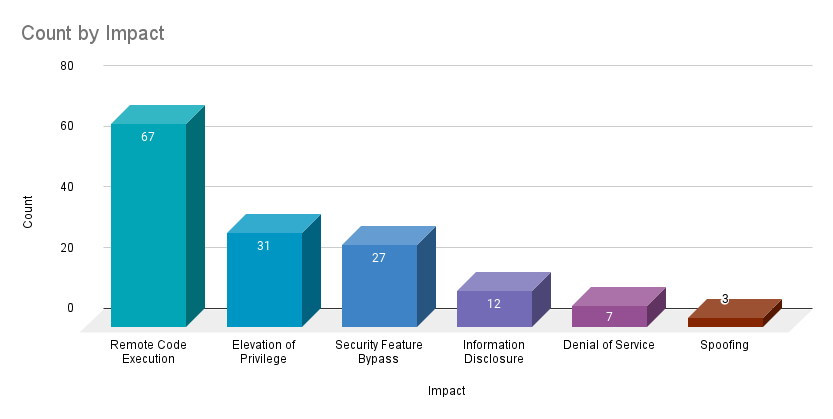
Remote code execution (RCE) vulnerabilities accounted for 45.6% of the vulnerabilities patched this month, followed by elevation of privilege (EoP) vulnerabilities at 21.1%.
CVE-2024-29988 | SmartScreen Prompt Security Feature Bypass Vulnerability
CVE-2024-29988 is a security feature bypass vulnerability in Microsoft Defender SmartScreen. It was assigned a CVSSv3 score of 8.8 and is rated as important. An attacker could exploit this vulnerability by convincing a target to open a specially crafted file using social engineering tactics such as an external link or malicious attachment sent over email, instant messages or social media. This flaw was reported to Microsoft by some of the same researchers that disclosed CVE-2024-21412, an Internet Shortcut Files security feature bypass that was associated with a DarkGate campaign using fake installer files impersonating Apple iTunes, Notion, NVIDIA and others.
The Zero Day Initiative (ZDI) says one of the researchers credited with reporting this flaw through ZDI discovered it being exploited in the wild as a zero-day. However, Microsoft has yet to update its advisory to reflect this finding. We will update this blog once Microsoft confirms exploitation.
CVE-2024-26234 | Proxy Driver Spoofing Vulnerability
CVE-2024-26234 is a spoofing vulnerability in the Proxy Driver of Microsoft Windows. It was assigned a CVSSv3 score of 6.7 and is rated as important. Initially, Microsoft did not flag this as being exploited. However, researchers at Sophos published a blog post that confirmed exploitation, which is now reflected in the Microsoft advisory for this vulnerability. According to Sophos, this was bundled as part of a fake Android Screen Mirroring application, LaiXi, which was signed using the Microsoft Windows Hardware Compatibility Program (WHCP). It has now been added to the Windows Driver.STL revocation list.
CVE-2024-29990 | Microsoft Azure Kubernetes Service Confidential Container Elevation of Privilege Vulnerability
CVE-2024-29990 is an EoP vulnerability in the Azure Kubernetes Service Confidential Containers (AKSCC). It was assigned a CVSSv3 score of 9 and is rated important. Exploitation of this flaw hinges on the preparation of a target environment by an attacker. Successful exploitation would enable an attacker to “steal credentials and affect resources beyond the security scope managed by AKSCC.” This includes taking over both “confidential guests and containers beyond the network stack it might be bound to.”
This is the third month in a row that a flaw in AKSCC was patched as part of Patch Tuesday:
| CVE | Description | CVSSv3 | Patch Tuesday |
|---|---|---|---|
| CVE-2024-21400 | Microsoft Azure Kubernetes Service Confidential Container Elevation of Privilege Vulnerability | 9 | March 2024 |
| CVE-2024-21376 | Microsoft Azure Kubernetes Service Confidential Container Remote Code Execution Vulnerability | 9 | February 2024 |
| CVE-2024-21403 | Microsoft Azure Kubernetes Service Confidential Container Elevation of Privilege Vulnerability | 9 | February 2024 |
All four of these vulnerabilities were reported to Microsoft by Yuval Avrahami of Palo Alto Networks.
41 CVEs | Microsoft ODBC Driver, WDAC OLE DB Driver and OLE DB Driver for SQL Server Remote Code Execution Vulnerability
This month's release included 41 CVEs affecting multiple drivers for SQL Server, the Open Database Connectivity (ODBC) driver, WDAC OLE DB Driver and OLE DB driver. All but one of these CVEs received CVSSv3 scores of 8.8, with the lone exception, CVE-2024-29045 receiving a 7.5. All were rated as “Exploitation Less Likely” according to the Microsoft Exploitability Index, with none being publicly disclosed or exploited in the wild. A full list of the CVEs is included in the table below.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2024-28929 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28930 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28931 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28932 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28933 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28934 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28935 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28936 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28937 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28938 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28941 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28943 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29043 | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28906 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28908 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28909 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28910 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28911 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28912 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28913 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28914 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28915 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28926 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28927 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28939 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28940 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28942 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28944 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-28945 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29044 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29045 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 7.5 |
| CVE-2024-29047 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29048 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29982 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29983 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29984 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29985 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-26210 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-26214 | Microsoft WDAC SQL Server ODBC Driver Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-26244 | Microsoft WDAC OLE DB Provider for SQL Server Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-29046 | Microsoft OLE DB Driver for SQL Server Remote Code Execution Vulnerability | 8.8 |
24 CVEs | Secure Boot Security Feature Bypass Vulnerability
Microsoft patched 24 CVEs in Windows Secure Boot in as part of the April 2024 Patch Tuesday release. All are rated as “Exploitation Less Likely” and vary in CVSSv3 scores from 4.1 to 8.0.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2024-26240 | Secure Boot Security Feature Bypass Vulnerability | 8 |
| CVE-2024-26189 | Secure Boot Security Feature Bypass Vulnerability | 8 |
| CVE-2024-28925 | Secure Boot Security Feature Bypass Vulnerability | 8 |
| CVE-2024-26180 | Secure Boot Security Feature Bypass Vulnerability | 8 |
| CVE-2024-29061 | Secure Boot Security Feature Bypass Vulnerability | 7.8 |
| CVE-2024-28920 | Secure Boot Security Feature Bypass Vulnerability | 7.8 |
| CVE-2024-26175 | Secure Boot Security Feature Bypass Vulnerability | 7.8 |
| CVE-2024-28896 | Secure Boot Security Feature Bypass Vulnerability | 7.5 |
| CVE-2024-26194 | Secure Boot Security Feature Bypass Vulnerability | 7.4 |
| CVE-2024-20688 | Secure Boot Security Feature Bypass Vulnerability | 7.1 |
| CVE-2024-29062 | Secure Boot Security Feature Bypass Vulnerability | 7.1 |
| CVE-2024-20689 | Secure Boot Security Feature Bypass Vulnerability | 7.1 |
| CVE-2024-28897 | Secure Boot Security Feature Bypass Vulnerability | 6.8 |
| CVE-2024-26168 | Secure Boot Security Feature Bypass Vulnerability | 6.8 |
| CVE-2024-28919 | Secure Boot Security Feature Bypass Vulnerability | 6.7 |
| CVE-2024-26250 | Secure Boot Security Feature Bypass Vulnerability | 6.7 |
| CVE-2024-20669 | Secure Boot Security Feature Bypass Vulnerability | 6.7 |
| CVE-2024-28924 | Secure Boot Security Feature Bypass Vulnerability | 6.7 |
| CVE-2024-26171 | Secure Boot Security Feature Bypass Vulnerability | 6.7 |
| CVE-2024-28921 | Secure Boot Security Feature Bypass Vulnerability | 6.7 |
| CVE-2024-28923 | Secure Boot Security Feature Bypass Vulnerability | 6.4 |
| CVE-2024-28898 | Secure Boot Security Feature Bypass Vulnerability | 6.3 |
| CVE-2024-28922 | Secure Boot Security Feature Bypass Vulnerability | 4.1 |
Four of the 24 CVEs were assigned a CVSSv3 score of 8.0. They include CVE-2024-26240, CVE-2024-26189, CVE-2024-28925 and CVE-2024-26180. Exploitation of all of these flaws do require an attacker to have either physical access or local administrator privileges on the vulnerable device.
These 24 CVEs are the first bundle of Secure Boot vulnerabilities we’ve seen since May 2023, when Microsoft patched CVE-2023-24932, another security feature bypass flaw in Secure Boot that was exploited in the wild as part of the BlackLotus UEFI bootkit.
Tenable Solutions
A list of all the plugins released for Tenable’s April 2024 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
For more specific guidance on best practices for vulnerability assessments, please refer to our blog post on How to Perform Efficient Vulnerability Assessments with Tenable.
Change Log
Update April 10: The blog has been updated to include reference to exploitation for CVE-2024-29988 and the addition of CVE-2024-26234.
Get more information
- Microsoft's April 2024 Security Updates
- Tenable plugins for Microsoft April 2024 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
Related Articles
- Exposure Management
- Vulnerability Management
- Exposure Management




