SecurityCenter Innovation Continues with 5.7 Release

Note: Tenable SecurityCenter is now Tenable.sc. To learn more about this application and its latest capabilities, visit the Tenable.sc web page.
As digitization continues and companies invest in a highly mobile workforce, it’s important they have a VM solution with automated, continuous and accurate visibility into their IT assets in order to meet their growing needs.
We recently shared how we’re invested in driving SecurityCenter innovation forward to support the growing needs of cybersecurity teams. As we continue on this path of innovation, we’re excited to share how we’re enhancing the platform with SecurityCenter 5.7. First, we’ve added a new mobile agent workforce feature to ensure proper correlation of IP addresses to assets. Next, we’ve updated the Common Vulnerability Scoring System used by the platform. These enhancements distinguish SecurityCenter as the VM solution to help cybersecurity professionals efficiently prioritize security risks and provide a clear view of their organization's security posture. continues and companies invest in a highly mobile workforce, it’s important they have a VM solution with automated, continuous and accurate visibility into their IT assets in order to meet their growing needs.
Mobile Agent Workforce
In today’s highly dynamic environment, a single IP address no longer uniquely identifies an asset. For example, my laptop’s IP address changes as it moves from my home office to the corporate network and then to a hotel. If vulnerability scans are performed when my laptop is connected at these different locations, my laptop would be identified as three different devices and create a separate record for each identified device.
The Mobile Agent Workforce feature in SecurityCenter 5.7 ensures proper correlation of IP addresses to assets. Assets with Nessus Agents installed are each assigned a unique UUID. Each IP address will be properly mapped to the unique UUID and its corresponding asset, giving users an accurate understanding of their inventory and the ability to create precise remediation lists.
Fig. 1
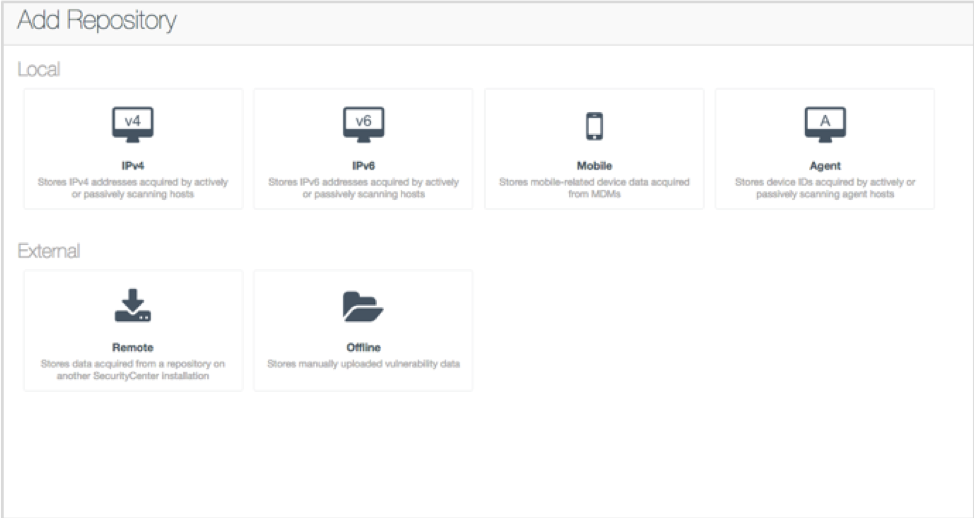
Fig. 2
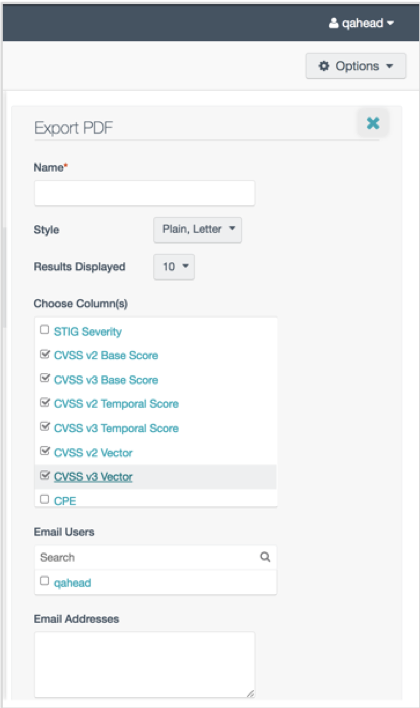
Figs. 1 and 2: Mobile Agent Workforce feature in SecurityCenter 5.7 ensures proper correlation of IP addresses to assets with a new agent repository type for agent scan data.
CVSS v3
Information security professionals continuously perform risk assessments of their environment to focus remediation efforts on the areas with the biggest security risk. Proper prioritization of remediation efforts depends a great deal on the metrics used to assess risk.
The main method SecurityCenter uses to assess risk is the Common Vulnerability Scoring System (CVSS). To advance the clarity, consistency and accuracy of scores for modern-day vulnerabilities, SecurityCenter 5.7 will pull vulnerability information from CVSS v3, the latest version of CVSS. This latest version includes additional attributes, such as scope and user interaction, to accurately reflect the severity and impact of a vulnerability in a customer's environment.
Fig. 3
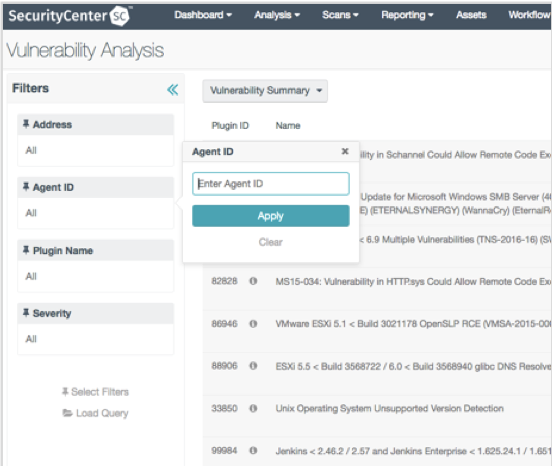
Fig. 3: CVSS v3 provides clearer, more consistent and more accurate scores for modern-day vulnerabilities.
SecurityCenter 5.7 is available now for customer download. Here's how to learn more:
- Current users can review the SecurityCenter 5.7 release notes, or the official documentation.
- To see SecurityCenter 5.7 for yourself, or speak with a Tenable sales representative, please request a demo.
- Visit our website for more about SecurityCenter, including whitepapers and reports.
Related Articles
- SecurityCenter
- Vulnerability Management
- Vulnerability Scanning








